Securely Cloud Data Storage and Sharing

DOI:
https://doi.org/10.54060/jieee.2024.66Keywords:
key distribution, private key, cloud server, cloud computing, outsourcingAbstract
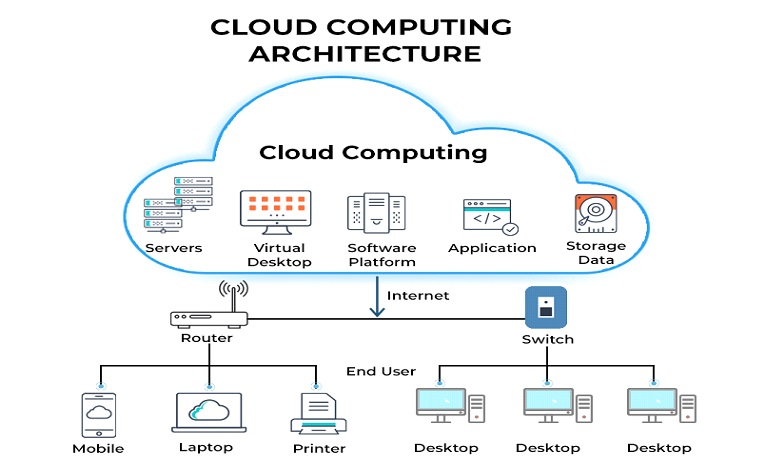
With the increasing adoption of cloud computing, data storage and sharing have be-come integral parts of our digital lives. However, ensuring the security and privacy of data stored in the cloud remains a significant challenge. This paper proposes a novel approach for securely storing and sharing data in the cloud, addressing the vulnerabilities associated with traditional cloud storage models. The proposed approach utilizes advanced cryptographic techniques, including hyperchaotic encryption and hash functions, to protect the confidentiality and integrity of data stored in the cloud. The hyperchaotic encryption algorithm provides a high level of security by introducing chaos-based dynamics into the encryption process, making it resistant to various attacks. Additionally, the hash function ensures the integrity of data by generating unique identifiers for each file stored in the cloud. To enhance data sharing security, the proposed approach employs access control mechanisms and user authentication protocols. Access control rules are enforced to restrict unauthorized access to data, while user authentication ensures that only legitimate users can access and modify the shared data.
Downloads
References
P. Sharma, M. D. Borah, and S. Namasudra, "Improving security of medical big data by using Blockchain technology," Computers & Electrical Engineering, vol. 96, p. 107529, 2021.
T. P. Ezhilarasi, N. Sudheer Kumar, T. P. Latchoumi, and N. Balayesu, "A secure data sharing using IDSS CP-ABE in cloud storage," in Advances in Industrial Automation and Smart Manufacturing, Springer, Singapore, 2021, pp. 1073-1085.
Y. Chen, L. Meng, H. Zhou, and G. Xue, "A blockchain-based medical data sharing mechanism with attribute-based access control and privacy protection," Wireless Communications and Mobile Computing, 2021.
C. Ge, W. Susilo, J. Baek, Z. Liu, J. Xia, and L. Fang, "A verifiable and fair attribute-based proxy re-encryption scheme for data sharing in clouds," IEEE Transactions on Dependable and Secure Computing, vol. 19, no. 5, pp. 2907-2919, 2021.
R. Sivan and Z. A. Zukarnain, "Security and privacy in cloud-based e-health system," Symmetry, vol. 13, no. 5, p. 742, 2021.
N. Eltayieb, R. Elhabob, A. Hassan, and F. Li, "A blockchain-based attribute-based signcryption scheme to secure data sharing in the cloud," Journal of Systems Architecture, vol. 102, p. 101653, 2020.
P. Sun, "Security and privacy protection in cloud computing: Discussions and challenges," Journal of Network and Computer Applications, vol. 160, p. 102642, 2020.
C. Ge, W. Susilo, Z. Liu, J. Xia, P. Szalachowski, and L. Fang, "Secure keyword search and data sharing mechanism for cloud computing," IEEE Transactions on Dependable and Secure Computing, vol. 18, no. 6, pp. 2787-2800, 2020.
T. Bhatia, A. K. Verma, and G. Sharma, "Towards a secure incremental proxy re‐encryption for e‐healthcare data sharing in mobile cloud computing," Concurrency and Computation: Practice and Experience, vol. 32, no. 5, p. e5520, 2020.
D. Zheng, B. Qin, Y. Li, and A. Tian, "Cloud-assisted attribute-based data sharing with efficient user revocation in the internet of things," IEEE Wireless Communications, vol. 27, no. 3, pp. 18-23, 2020.
H. Li, C. Lan, X. Fu, C. Wang, F. Li, and H. Guo, "A secure and lightweight fine-grained data sharing scheme for mobile cloud computing," Sensors, vol. 20, no. 17, p. 4720, 2020.
G. Elavarasan and S. Veni, "Data Sharing Attribute-Based Secure with Efficient Revocation in Cloud Computing," in 2020 International Conference on Computing and Information Technology (ICCIT-1441), IEEE, September 2020, pp. 1-6.
M. A. Islam and S. Madria, "Attribute-based encryption scheme for secure multi-group data sharing in cloud," IEEE Transactions on Services Computing, 2020.
N. Eltayieb, P. Wang, A. Hassan, R. Elhabob, and F. Li, "ASDS: Attribute‐based secure data sharing scheme for reliable cloud environment," Security and Privacy, vol. 2, no. 2, p. e57, 2019.
S. Namasudra, "An improved attribute‐based encryption technique towards data security in cloud computing," Con-currency and Computation: Practice and Experience, vol. 31, no. 3, p. e4364, 2019.
S. Han, K. Han, and S. Zhang, "A data sharing protocol to minimize security and privacy risks of cloud storage in big data era," IEEE Access, vol. 7, pp. 60290-60298, 2019.
S. Nalajala, K. Akhil, V. Sai, D. C. Shekhar, and P. Tumuluru, "Light weight secure data sharing scheme for mobile cloud computing," in 2019 Third International conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud)(I-SMAC), IEEE, December 2019, pp. 613-617.
J. Li, Y. Zhang, X. Chen, and Y. Xiang, "Secure attribute-based data sharing for resource-limited users in cloud compu-ting," Computers & Security, vol. 72, pp. 1-12, 2018.
A. Wu, D. Zheng, Y. Zhang, and M. Yang, "Hidden policy attribute-based data sharing with direct revocation and key-word search in cloud computing," Sensors, vol. 18, no. 7, p. 2158, 2018.
Y. Zhang, A. Wu, and D. Zheng, "Efficient and privacy-aware attribute-based data sharing in mobile cloud computing," Journal of Ambient Intelligence and Humanized Computing, vol. 9, no. 4, pp. 1039-1048, 2018.
Q. Huang, W. Yue, Y. He, and Y. Yang, "Secure identity-based data sharing and profile matching for mobile healthcare social networks in cloud computing," IEEE Access, vol. 6, pp. 36584-36594, 2018.
M. Sookhak, F. R. Yu, M. K. Khan, Y. Xiang, and R. Buyya, "Attribute-based data access control in mobile cloud compu-ting: Taxonomy and open issues," Future Generation Computer Systems, vol. 72, pp. 273-287, 2017.
A. Alotaibi, A. Barnawi, and M. Buhari, "Attribute-based secure data sharing with efficient revocation in fog compu-ting," Journal of Information Security, vol. 8, no. 03, p. 203, 2017.
A. Sara, Y. Tassnim, and M. Abdellatif, "Secure confidential big data sharing in cloud computing using KP-ABE," in Proceedings of the 2nd international Conference on Big Data, Cloud and Applications, 2017, pp. 1-4.
N. S. B. Johari, "Improving Security and Efficiency In Attribute Based Data Sharing,"
Downloads
Published
How to Cite
CITATION COUNT
License
Copyright (c) 2024 Neelesh Jain, Nishant kumar, Prateek Singhal

This work is licensed under a Creative Commons Attribution 4.0 International License.